This series of articles is a compilation of the notes I gathered during my programming bootcamp at Green Fox Academy, last year.
You can read the first article here:
Tokens
The general concept behind a token-based authentication system is simple. Allow users to enter their username and password in order to obtain a token which allows them to fetch a specific resource — without using their username and password. Once their token has been obtained, the user can offer the token — which offers access to a specific resource for a time period — to the remote site.
Advantages of a token-based authentication system
In a token-based authentication system, there is no concept of a session. Sessions are used in a cookie-based environment. With regards to tokens, there is no session as such.
· Easy to scale
· Faster
· Secure
· Token based authentication systems work well in a web API environment where most applications are available via their APIs
JWT (JSON Web Token) Tokens

JSON Web Token (JWT) is an open standard that defines a compact and self-contained way for securely transmitting information between parties as a JSON object.
Use-cases for JWT Tokens
· Authorization: This is the most common scenario for using JWT and includes situations like the Single Sign On feature.
· Information Exchange: JWTs can be signed, so you can be sure the senders are who they say they are. Additionally, as the signature is calculated using the header and the payload, you can also verify that the content hasn’t been tampered with.
JSON Web Token structure:
In its compact form, JSON Web Tokens consist of three parts separated by dots:
1. Header
2. Payload
3. Signature
Header
The header typically consists of two parts: the type of the token, which is JWT, and the signing algorithm being used, such as HMAC SHA256 or RSA.
{“alg”: “HS256”,
“typ”: “JWT”}
Payload
The second part of the token is the payload, which contains the claims. Claims are statements about an entity (typically, the user) and additional data. There are three types of claims: registered, public, and private claims.
{“sub”: “1234567890”,
“name”: “John Doe”,
“admin”: true}
Signature
To create the signature part, you have to take the encoded header, the encoded payload, a secret, the algorithm specified in the header, and sign that. For example, if you want to use the HMAC SHA256 algorithm, the signature will be created in the following way:
HMACSHA256(
base64UrlEncode(header) + “.” +
base64UrlEncode(payload),
secret)
The signature is used to verify the message wasn’t changed along the way, and, in the case of tokens signed with a private key, it can also verify that the sender of the JWT is who it says it is.
The following shows a JWT that has the previous header and payload encoded, and it is signed with a secret:

How do JSON Web Tokens work?
In authentication, when the user successfully logs in using their credentials, a JSON Web Token will be returned. Since tokens are credentials, great care must be taken to prevent security issues. In general, you should not keep tokens longer than required.
Whenever the user wants to access a protected route or resource, the user agent should send the JWT, typically in the Authorization header using the Bearer schema. The content of the header should look like the following:
Authorization: Bearer <token>
Refresh Tokens
Refresh tokens carry the information necessary to get a new access token. In other words, whenever an access token is required to access a specific resource, a client may use a refresh token to get a new access token issued by the authentication server.
Authentication vs Authorization
401 — Unauthorized
VS
403 — Forbidden
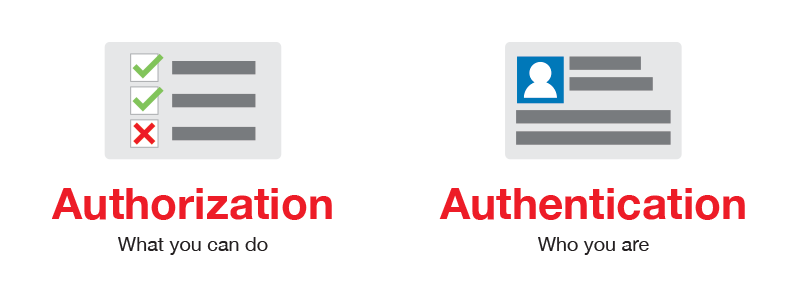
Authentication is different from authorization.
When you get a 401 response, Unauthorized, it means you are not authenticated — either not at all or with wrong credentials. It is something temporary that you can fix by providing the right combination of username and password.
On the other hand, a 403 response, Forbidden, means that you are authenticated but you are not authorized to see the resource you’re requesting. You might be a regular user and trying to see a part of the application that is only for admin users, for example.

📝 Read this story later in Journal.
👩💻 Wake up every Sunday morning to the week’s most noteworthy stories in Tech waiting in your inbox. Read the Noteworthy in Tech newsletter.